Chainalysis Caught Running Fake Bitcoin Nodes
 Chainalysis got caught running 250 fake Bitcoin nodes. Maybe they would have gotten away with it if they hadn’t been slowing down transactions that involved Breadwallet clients. Now that they have been exposed, they deny that they’ve been deliberately running a kind of attack called a “Sybil attack.” They claim that what they call a “partial Sybil attack” was an unintended side effect of tests of a product that would have helped Bitcoin companies stay compliant with local regulations.
Chainalysis got caught running 250 fake Bitcoin nodes. Maybe they would have gotten away with it if they hadn’t been slowing down transactions that involved Breadwallet clients. Now that they have been exposed, they deny that they’ve been deliberately running a kind of attack called a “Sybil attack.” They claim that what they call a “partial Sybil attack” was an unintended side effect of tests of a product that would have helped Bitcoin companies stay compliant with local regulations.
Even if it was unintentional, it annoyed some Bitcoin users. Imagine how the chairman of the U.S. Federal Reserve would have reacted if somebody had been spoofing servers owned or rented by the Reserve so they could intercept information about transactions between banks and the Reserve. The fake servers could even have carried out fake transactions and damaged the reputation of the Federal Reserve’s internal network. How would a client tell the difference between a fake server and a real one? That’s the Sybil Attack and the chairman would not have been very impressed by claims that it was a test of a new product that only incidentally intercepted data that would theoretically only be the business of the banks and the Federal Reserve.
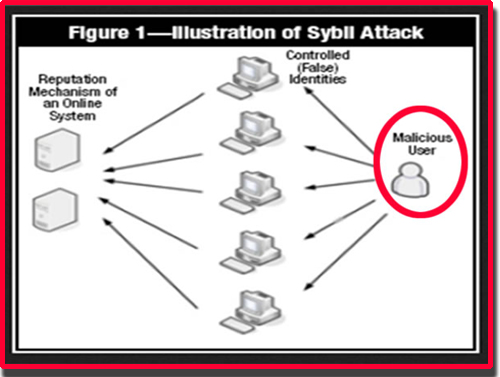
How The Sybil Attack Works
In the Chainalysis case, a client would not have known the difference between one of the 6,489 genuine nodes and the 250 fake nodes. Some Bitcoin insiders have even opined that Chainalysis may have violated laws like the U.S. Computer Fraud and Abuse Act by effectively hacking the Bitcoin network in a way that would have made it difficult for genuine Bitcoin nodes to communicate with one another and with clients. Core developer Peter Todd said of the Sybil attack, “It’d be ironic if a service ostensibly intending to help with regulatory compliance did so by violating laws against disrupting and hacking networks.”
Although Chainalysis does claim that they have received requests for help in tracking down stolen Bitcoin, the critics seem to outnumber the people who think Chainalysis was only guilty of attempting a test of its product that had unintended results. Bitcointalk members were the first to notice the fake nodes, calling it “pretty weird behavior” that a single subnet from France would appear to be monitoring the Bitcoin network. Even before the name of Chainalysis came to light, they were discussing the possibility that this was “a rather ham-fisted Sybil attack” amid some high-end computer networking technobabble.
“They’ve made themselves known,” said one Reddit commenter who warned that Chainalysis is “up to no good. … If they wanted to do passive monitoring, they wouldn’t be tarpitting nodes that connect to them.” Chainalysis was mostly caught out because it was preventing some Simplified Payment Verification clients from syncing up to the genuine Bitcoin network.
However, other Redditors were quick to point out that the Sybil attack simply exploited a vulnerability in the Bitcoin network that might have been overlooked: “The fact that it’s even possible to do surveillance is an issue you should address to the core developers.” It’s possible that Chainalysis might not even be involved in the next, more sophisticated Sybil attack now that their attempt to clone Bitcoin nodes brought this particular security vulnerability to light. Now that it is visible, Bitcoin core developers should make countering Sybil attacks a priority before a more sophisticated spoof of Bitcoin nodes is created.
A Discussion Of Sybil Attacks
This apparently has more to do with a program for traffic control than Bitcoin. However, it can also be used as a model for preventing future Sybil attacks against Bitcoin.
Keep Yourself Secure
[simple-rss feed=”http://rest.ebay.com/epn/v1/find/item.rss?keyword=%28sybil+attack%2Ccomputer+security%29&sortOrder=BestMatch&programid=1&campaignid=5337337555&toolid=10039&listingType1=All&lgeo=1&feedType=rss” limit=10]








