IP Addressing
Each device on a network must have a unique IP address in order to communicate over a network. If more than one device have the same address, devices that must deliver data to that IP address will become confused. Some IP addresses are reserved for connecting an interior network to the exterior world (the IP address that the Internet sees), broadcast addresses used for sending packets to all devices on a network or subnet, and addresses that network administrators use for testing and troubleshooting.
Each IP address also must have an accompanying subnet mask that provides necessary information to network devices such as routers. Subnet masks make it possible to divide large networks into smaller, more manageable subnets.
Address Classes
With the addition of technologies and protocols such as subnet masking and VSLM, address classes aren’t as significant on modern networks as they once were. Address classes are still useful for:
- Getting your certification
- Handling some “legacy” technologies that have been around since the 1990s
- Discussing IP address groups
- Discussing which octets can and can’t be used for subnetting
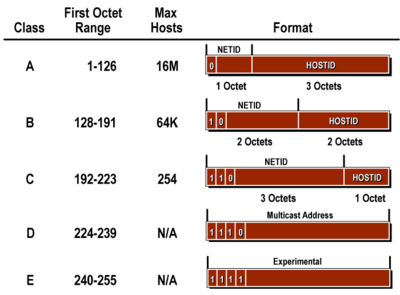
When you are actually maintaining a network for your organization, you’ll mostly see networks that can be classified as Class A, Class B and Class C. Class A addressing has a first octet between 1 and 126 and is most commonly used for large networks. IP addresses with a first octet of 127 are reserved for special purposes. 127.0.0.1 is used to test whether a machine’s TCP/IP is functional. A Class B network can use the numbers 128 through 191 for its first octets. Class C networks use IP addresses with the first octet between 192 and 223. Class D addresses are used for multicasting and Class E is used for experimental purposes.
Subnet Masks
For this part, it will be useful to understand octets. Essentially, octets are each grouping of eight bits in an IP address or subnet mask. Networks will see a typical Class A subnet as 11111111.00000000.00000000.00000000, which translates into a more human-readable form as 255.0.0.0.
Subnet masks identify the octets that define the network and the ones used to identify a specific device on the network. Each address class has its own default subnet mask with the bits in each octet being either all on (255) or all off (0). The typical rule is that, if all the bits are turned on in a default subnet mask octet (255), that octet is reserved for the network in the IP address. If all bits are turned off (0), that octet is reserved for hosts in the IP address. Each subnet mask is associated with a specific class, as in the chart below:
There will always be at least two reserved addresses on each network. The network number cannot be used for individual hosts. The network number will typically have all the bits in the host portion turned off, such as 10.0.0.0 or 192.168.1.0. The broadcast number for each network and/or subnet also cannot be used for hosts. This address will typically have all the bits in the host portion turned on, such as 10.255.255.255 or 172.30.255.255.
Using IP Addresses
If you’ve been into networking for a while, you might have heard of the risk that IPv4 addresses being “used up” as computers and other devices that can connect to networks become more prevalent. You also know that there have been attempts to work around this problem, such as introducing an updated version of IP called IPv6 and making use of private IP addresses.
Private IP addressing was created with two Requests For Comment (RFC), 1918 and 4193, and reserves one range of addresses in each class for use in internal networking. The Class A private address range is 10.x.x.x; the Class B range is 172.16.x.x through 172.31.x.x; and the Class C range is 192.168.x.x. These address ranges are for your private network only and can’t be used as the IP address that the Internet sees.
Subnetting
Subnetting is a way to steal bits of an IP address so that you can carve up a network into smaller segments. This makes your network easier to manage and troubleshoot and also makes routing packets over a network more efficient. The main thing to remember is that you can borrow bits from the host portion of an IP address, but not the network portion. This makes using the Class A 10.x.x.x as a private address range very popular for network administrators who must manage a large and/or rapidly growing network.
For the Class A network, you start by turning on bits from the second octet in the default subnet mask, 255.0.0.0 or 11111111.00000000.00000000.00000000 in binary. With two bits turned on, the second binary should look like 11000000, which translates as 192 in the decimal system. The subnet mask should now look like 255.192.0.0.
To calculate the number of potential subnets, you go back to the number of bits you borrowed and make that the “power” in the “powers of 2” chart familiar to any network specialist. Because you borrowed two bits, you calculate for 22, which translates as four potential subnets. I say “potential” because it’s not uncommon for network administrators to actually use three, seven or ten subnets – some number that isn’t a convenient power of two. The leftover subnets provide room for expansion as needed.
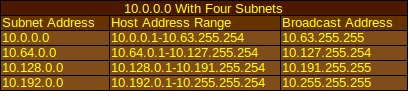
Those four subnets are divided up into equal parts with an equal number of IP addresses. On each subnet, one address will be reserved as the subnet address and one will be reserved for the broadcast address, as seen in this chart:
That means eight reserved IP addresses, but these four subnets are going to be large enough that you aren’t likely to miss them (to the tune of 4,194,302 available host IP addresses, as told by this subnet calculator!). If you’re going for a Class A internal network, your organization is probably big enough that you want more than four subnets.
Classless Inter-Domain Routing
Classless Inter-Domain Routing (CDIR) provides a method to create blocks of IP addresses and route data packets. It uses slash address notation as a shorthand method for denoting subnet masks. For example, the subnet mask 255.255.0.0 has sixteen bits turned on, so network administrators might write it down as /16 after the IP address they just set for a router. A subnet mask with “borrowed bits” from a subnetting problem, such as 255.255.240.0 with four bits turned on in the third octet, would be written as /20. Most network specialists use it to save time when documenting settings for their devices and communicating with colleagues.
Everything You Ever Wanted To Know About IP Addressing in One Book
More Supplies for Networking
[simple-rss feed=”http://rest.ebay.com/epn/v1/find/item.rss?keyword=Cisco+certification&categoryId1=58058&sortOrder=BestMatch&programid=1&campaignid=5337337555&toolid=10039&listingType1=All&lgeo=1&feedType=rss” limit=6]